Configuring DMZ Host
The DMZ Host feature allows you to direct unsolicited inbound traffic to a specific LAN device (the DMZ Host) such as a computer running a web server or other internal application. Enabling DMZ Host is particularly useful for certain services like VPN, NetMeeting, and streaming video where the remote server may require a WAN connection to the LAN device rather than being NATed by the router.
You can configure the DMZ Host settings to give the device access to devices on other LAN bridges, or to keep the DMZ Host isolated on its own LAN bridge.
DMZ Host is disabled by default. You should be aware of the security risk of allowing a host device on your LAN to be exposed to the Internet in this way. The DMZ Host device will have all TCP and UDP ports open and be exposed to traffic and potential attacks that would normally be blocked by your firewall settings. Ensure that the DMZ Host device has all security-related patches and updates installed.

To configure DMZ Host:
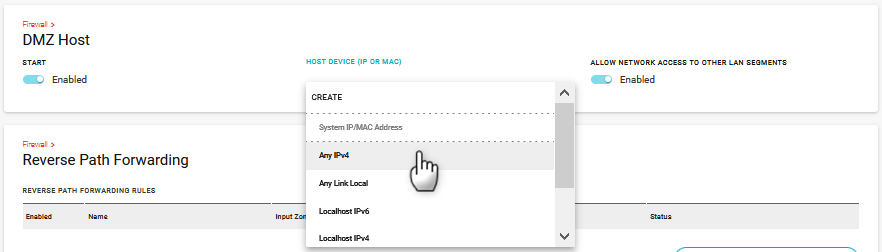
Go to Networking > Firewall > DMZ Host.
Under START, click the switch to enable DMZ Host.
Under HOST DEVICE (IP OR MAC), select the device to be the DMZ Host.
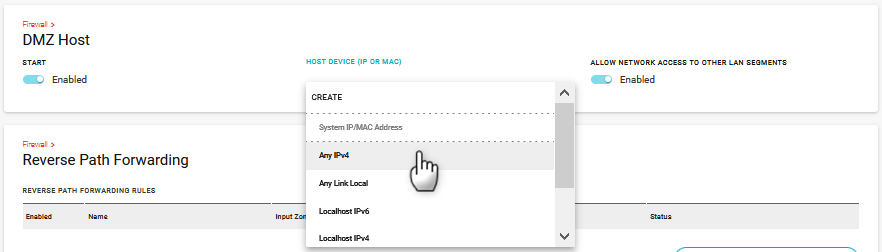
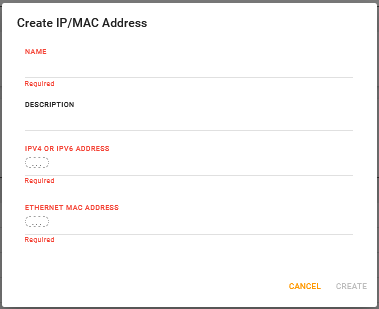
If none of the default options meet your needs, click CREATE to configure your own DMZ Host in the Create IP/MAC Address screen.
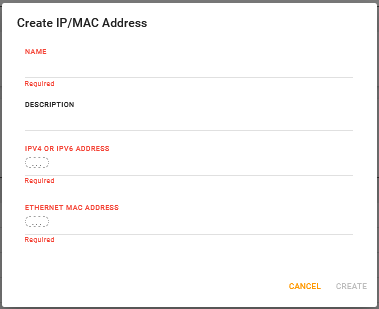
a. Enter a NAME and optional DESCRIPTION.
b. Enter the IPv4 or IPv6 LAN address for the device OR enter the ETHERNET MAC ADDRESS of the device.
c. Click CREATE.
Optional: If desired, under ALLOW NETWORK ACCESS TO OTHER LAN SEGMENTS, click the switch to enable.
If the DMZ Host has access to other LAN segments, any successful malware attacks on the DMZ Host device could potentially spread to other devices across your network. Even when access to other LAN segments is disabled, the DMZ Host can access other devices on the same LAN segment. To truly isolate the DMZ Host, Sierra Wireless recommends creating a LAN Bridge for the DMZ Host only.
 Searching...
Searching...