Configuring VPN
The router can act as a Virtual Private Network (VPN) device, providing enterprise VPN access to any device connected to the router even when a device has no VPN client capability on its own. The router supports up to five simultaneous IPsec VPN tunnels. The IPsec implementation is fully IKEv1 and IKEv2 compliant, and supports MOBIKE when operating over IKEv2. The AirLink OS VPN implementation also provides the option to configure IPsec tunnels to FIPS (Federal Information Processing Standards) mode.
You can configure VPN tunnels for LAN-terminated or Host-terminated applications. For Host-terminated applications, you must configure virtual IP settings that control how the router acquires a virtual IP address (automatically from the VPN server, or manually). For more information, see the See IPsec Configuration Settings below.
You cannot create a firewall rule that applies to outbound/inbound traffic inside an IPsec tunnel.
 Initializing Table Of Contents...
Initializing Table Of Contents...Client Mode and Server Mode Compared
You can configure the router as a VPN client or VPN server. The table below outlines how the router operates in each mode.
| SERVER MODE | CLIENT MODE | |
|---|---|---|
| Overall relationship | Master – sets all details for connection, for all clients. AirLink routers running AirLink OS can support multiple clients connected simultaneously and are limited only by the throughput requirements of those clients. | Slave – must match the defined details for a single connection as defined on the target server |
| Tunnel specifications | Server defines/sets the configuration: authentication mechanism and details, network details | Client must match a configuration set on the server to which it is connecting |
| Network communication | Server defines what “enterprise” or central network(s) are available to remote clients, and what the expected remote network connection will look like (LAN or Host termination) | Client provides the remote network segment in LAN termination and may provide the individual host address for Host termination if the server does not have the ability to assign one |
| Routing | Server advertises routing information to the central network to access remote clients | Client provides routing for remote clients to access the central network |
| Connection details | Accepts or rejects tunnel connection requests | Requests a tunnel connection |
IPsec Tunnel Configuration Settings
These are the settings you’ll find in the Basic Configuration Steps described below.
| SETTING | DESCRIPTION | DEFAULT SETTING | RANGE |
|---|---|---|---|
| NAME | Descriptive name for the tunnel | n/a | n/a |
| MODE |
Sets Client or Server mode for VPN operation. In Server mode, the router is configured to accept incoming tunnel requests and contains all details for all possible incoming connections. In Client mode, the router must match a unique configuration contained on the server to which it is connecting. |
Client | Client, Server |
| LAN/HOST MODE |
Select where the VPN tunnel terminates.
|
LAN | LAN, HOST |
| USE DEFAULT VIRTUAL IP POOL(S) | Appears when the tunnel is being configured for Server/HOST mode. | Enabled | Enabled, Disabled |
| VIRTUAL IP ADDRESS POOL(S) |
Appears when the tunnel is being configured for Server/HOST mode. In Server/HOST mode, the router allocates virtual IPv4 IP addresses from this pool. Note: Ensure that the Virtual IP address pool is uniquely routable in the network topology. The IP address range cannot be part of the network on the remote (Client) end. |
10.0.3.0/24 | IPv4 IP address |
| VIRTUAL IP ADDRESS POOL(S) |
Appears when the tunnel is being configured for Server/HOST mode. In Server/HOST mode, the router allocates virtual IPv6 IP addresses from this pool. Note: Ensure that the Virtual IP address pool is uniquely routable in the network topology. The IP address range cannot be part of the network on the remote (Client) end. |
2001:db8::3:0/24 | IPv6 IP address |
| CLIENT VIRTUAL IP TYPE | Appears when the tunnel is being configured for Client/HOST mode. Selects how the virtual IP address is assigned. In most applications, this is left at Automatic. | Automatic | Automatic (requests a virtual IP address from the server), Static |
| VIRTUAL IP ADDRESS |
Appears when the tunnel is being configured for Client/HOST mode. When CLIENT VIRTUAL IP TYPE is Static, this is a required field. Only one address of an IP family is allowed. When CLIENT VIRTUAL IP TYPE is Automatic, any IP addresses entered here are requested from the server. The server may not return the same virtual IP addresses. Note: Static virtual IP addresses are ignored by Sierra Wireless ACM. The ACM assigns a virtual IP address from the subnet configured in the ACM. |
n/a | n/a |
| IKE VERSION | Sets the Internet Key Exchange (IKE) mode. The default setting of IKEv2 is required for FIPS mode and MOBIKE. You may need to select IKEv1 when the router is in Client mode and a third-party VPN appliance is not compatible with IKEv2. | IKEv2 | IKEv2, IKEv1 |
| MULTIPLE SA’s FOR IKEV2 | Enables compatibility with Cisco VPNs when multiple remote subnets are used in a single child SA. If you define multiple remote subnets under REMOTE SUBNETS, enable this setting to create a separate child SA for each remote subnet. | Disabled | Disabled, Enabled |
| MOBIKE |
In IKEv2 mode, enabling MOBIKE allows a VPN tunnel to stay connected, even if the WAN interface used by the tunnel changes. For example, the tunnel stays connected if the WAN interface changes from Ethernet to cellular. Note:
|
Enabled | Enabled, Disabled |
| AUTHENTICATION TYPE | Sets the authentication type/method | Certificate | Certificate, PSK |
| CERTIFICATES |
When AUTHENTICATION TYPE is Certificate, lets you add or create/upload PEM certificates for authentication. 
|
n/a | n/a |
| PSK |
When AUTHENTICATION TYPE is PSK, lets you set the pre-shared key for authentication.
|
n/a | n/a |
| PEERS | Required to identify the peer side of a VPN connection. This is the primary peer (see SECONDARY PEER FOR FAILOVER below) and can be an IP address or an FQDN. | n/a | IPv4, IPv6 |
| LOCAL SUBNETS | Enter the local address or subnet in CIDR notation; for example, 192.168.13.0/24 | n/a | n/a |
| REMOTE SUBNETS |
The IP address or subnet (in CIDR notation) of the device(s) connected to the remote VPN server. These addresses/subnets will be accessible from any hosts connected locally to the router. To configure a full tunnel, enter 0.0.0.0/0. To configure a split tunnel, enter the individual remote subnets. Note: Not available when configuring the tunnel for Server/HOST mode. |
n/a | n/a |
| EXEMPT SUBNETS | List of Remote Addresses or subnets to be exempted. Traffic passing through the router to the IP addresses (or Fully Qualified Domain Names (FQDNs)) in this list is sent directly to the Internet (it is not sent through the IPsec VPN tunnel). | n/a | n/a |
| LOCAL AUTHENTICATION ID | You can enter the Local Authentication ID as a text string to identify the router as a VPN client. The Local Authentication ID must also be configured on the remote VPN server (the Sierra Wireless ACM, for example). Alternatively, you can leave the Local Authentication ID blank to use the default WAN IP address. The default WAN IP address would also need to be configured on the remote server/ACM. | n/a | n/a |
| REMOTE AUTHENTICATION ID | The Remote Authentication ID configures how the router recognizes incoming traffic. This setting must match the server side. | n/a | n/a |
| WAN INTERFACES |
Select the WAN interfaces to use for this tunnel, in order of priority (first to last/left to right). The order specifies the sequence of failover if the highest-priority WAN interface loses connection. You can select default to have the tunnel use the default WAN zone. In that case, the default WAN priority of Ethernet, Wi-Fi and Cellular applies. Please note that even when default is not selected, the tunnel will use the default WAN interface if no other configured WAN interface is available. |
List of enabled WAN Interfaces (varies by router model). | |
| START | Enable the IPsec tunnel and connect to the configured peer. Takes effect after you click CREATE. | Disabled | Disabled, Enabled |
| DEAD PEER DETECTION (DPD) |
Dead Peer Detection (DPD) verifies the status of the active connection, and can be configured to take action if the primary/active VPN tunnel goes down. Possible actions when DPD detects a failed connection are: * Restart (default): The router restarts the current IPsec tunnel. * None: The router takes no action. * Failover: The router begins using the SECONDARY PEER FOR FAILOVER. For more information, see VPN Failover. |
Restart | Restart, None, Failover |
| SECONDARY PEER FOR FAILOVER |
When DEAD PEER DETECTION is set to Failover, enter the secondary peer that will take over from the primary peer. This can be an IP address or an FQDN. 
|
n/a | n/a |
| DPD INTERVAL (SECONDS) | Sets the DPD interval (in seconds). If there has been no traffic during this interval, after five retries (each with an interval of 30 seconds by default) the router takes the DPD action configured above. | 30 | 30 - 3600 |
| IKE REKEY TIME (SECONDS) | Sets how long the VPN tunnel is active, in seconds | 7200 | 60 - 32000000 |
| IKE ENCRYPTION | Sets the type and length of encryption key used to encrypt/decrypt IKE packets. IKE Encryption is the first stage of encryption. More bits in the encryption key increases the security of the traffic, but this also increases the processing load and reduces the number of simultaneous clients the router can support. | aes256 |
|
| IKE INTEGRITY | Sets the type and length of digest used for authentication. | sha256 | sha256, sha384, sha512 |
| IKE DIFFIE-HELLMAN GROUPS |
Use this field to select the DH (Diffie-Hellman) group pre-shared key length used for authentication. The DH group number determines the length of the key used in the key exchange process. Longer keys are more secure, but take longer to compute. Also note that both peers in the VPN exchange must use the same DH group. |
dh16 (modp4096) |
|
| PERFECT FORWARD SECURITY (PFS) | PFS adds additional security because each session uses a unique temporary public/private key pair to generate the shared secret. One key cannot be derived from another. This ensures previous and subsequent encryption keys are secure, even if one key is compromised. | Enabled | Enabled, Disabled |
| ESP REKEY TIME (SECONDS) | Sets how long the VPN tunnel is active, in seconds | 7200 | 60 - 32000000 |
| ESP ENCRYPTION | Sets the type and length of encryption key used to encrypt/decrypt ESP (Encapsulating Security Payload) packets. ESP Encryption is the second stage of encryption. More bits in the encryption key increases the security of the traffic, but this also increases the processing load and reduces the number of simultaneous clients the router can support. | aes256 |
|
| ESP INTEGRITY | Sets the type and length of digest used for authentication | sha256 |
|
| ESP DIFFIE-HELLMAN GROUPS | Use this field to select the DH (Diffie-Hellman) group key length used for authentication. The DH group number determines the length of the key used in the key exchange process. Longer keys are more secure, but take longer to compute. Also note that both peers in the VPN exchange must use the same DH group. | dh16 (modp4096) |
|
Basic Configuration Steps
To begin configuring a VPN tunnel:
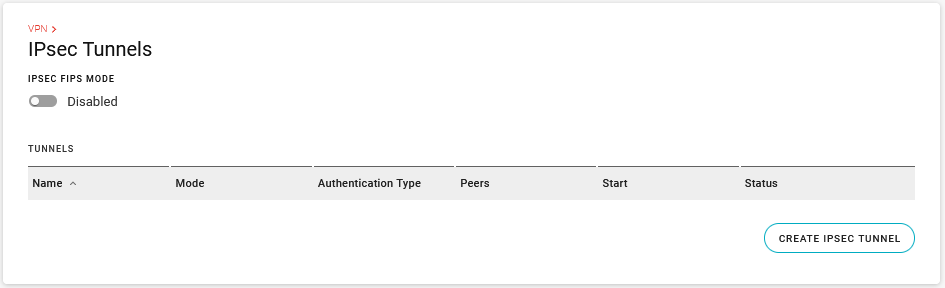
Go to Networking > VPN > IPsec Tunnels.
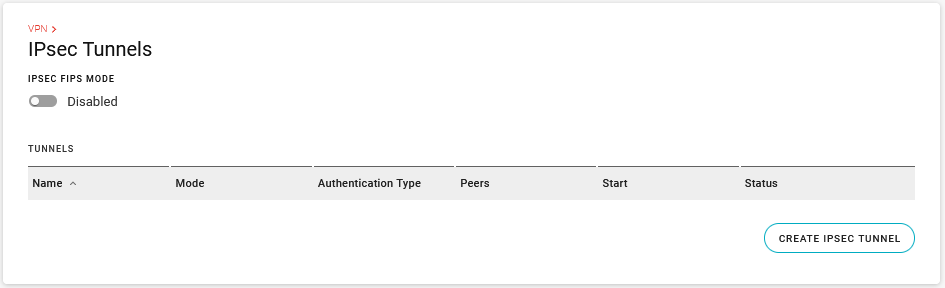
Enable IPSEC FIPS MODE, if required. When enabled, a FIPS-approved cryptographic module is used for IPsec data protection, and only FIPS-approved cryptographic algorithms are allowed for tunnel configurations. Note: FIPS is only supported for IKEv2 tunnels.
Click CREATE IPSEC TUNNEL.
Configure the router’s VPN mode and type of IPsec tunnel for your desired application. The following options are available:
- Client mode, LAN-to-LAN tunnel
- Client mode, HOST-to-LAN tunnel
- Server mode, LAN-to-LAN tunnel
- Server mode, HOST-to-LAN tunnel
Click CREATE.
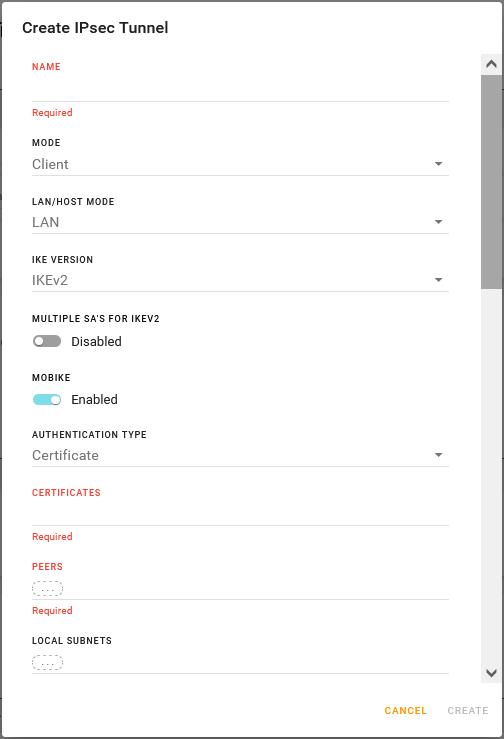
Configuring a LAN-to-LAN tunnel in Client mode
The settings in the procedure below are described in the IPsec Configuration Settings table above.
To configure a LAN-to-LAN tunnel in Client mode:
- Enter a tunnel NAME.
- Set the router’s VPN MODE to Client.
- Set the LAN/HOST MODE to LAN.
- Select the IKE VERSION. When IKE VERSION is set to IKEv2, you can enable or disable:
- MULTIPLE SA’S FOR IKEV2
- MOBIKE
- Select the AUTHENTICATION TYPE.
- After selecting Certificates, you must select any existing PEM Certificates on the router, or upload the certificate components to the router.
- After selecting PSK, you must enter a text string for the pre-shared key.
- Enter the PEERS as one or more IPv4 or IPv6 IP addresses.
- Enter LOCAL SUBNETS, REMOTE SUBNETS and any EXEMPT SUBNETS.
- Enter LOCAL AUTHENTICATION ID and REMOTE AUTHENTICATION ID to match the credentials for your VPN server.
- Select the WAN INTERFACES for VPN traffic to and from the router, in order of priority.
- Select whether to START the tunnel when you finish configuration and click CREATE.
- Configure DEAD PEER DETECTION, if desired (requires you to configure the SECONDARY PEER FOR FAILOVER).
- Configure IKE settings.
- Select whether to use PERFECT FORWARD SECURITY (PFS).
- If PFS is enabled, configure ESP settings.
- Click CREATE.
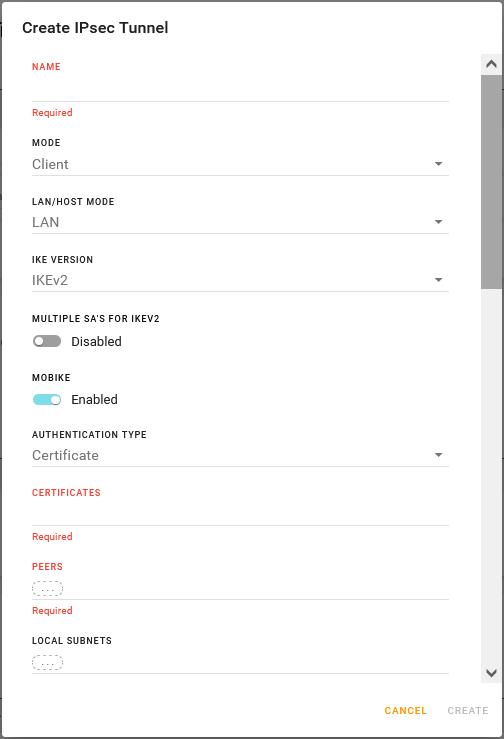
Configuring a HOST-to-LAN tunnel in Client mode
The settings in the procedure below are described in the IPsec Configuration Settings table above.
To configure a HOST-to-LAN tunnel in Client mode:
- Enter a tunnel NAME.
- Set the router’s VPN MODE to Client.
- Set the LAN/HOST MODE to HOST.
- Select the CLIENT VIRTUAL IP TYPE.
- Enter a VIRTUAL IP ADDRESS, if required by the CLIENT VIRTUAL IP TYPE.
- Select the IKE VERSION. When IKE VERSION is set to IKEv2, you can enable or disable:
- MULTIPLE SA’S FOR IKEV2
- MOBIKE
- Select the AUTHENTICATION TYPE.
- After selecting Certificates, you must select any existing PEM Certificates on the router, or upload the certificate components to the router.
- After selecting PSK, you must enter a text string for the pre-shared key.
- Enter the PEERS as one or more IPv4 or IPv6 IP addresses.
- Enter LOCAL SUBNETS, REMOTE SUBNETS and any EXEMPT SUBNETS.
- Enter LOCAL AUTHENTICATION ID and REMOTE AUTHENTICATION ID to match the credentials for your VPN server.
- Select the WAN INTERFACES for VPN traffic to and from the router, in order of priority.
- Select whether to START the tunnel when you finish configuration and click CREATE.
- Configure DEAD PEER DETECTION, if desired (requires you to configure the SECONDARY PEER FOR FAILOVER).
- Configure IKE settings.
- Select whether to use PERFECT FORWARD SECURITY (PFS).
- If PFS is enabled, configure ESP settings.
- Click CREATE.
Configuring a LAN-to-LAN tunnel in Server mode
The settings in the procedure below are described in the IPsec Configuration Settings table above.
To configure a LAN-to-LAN tunnel in Server mode:
- Enter a tunnel NAME.
- Set the router’s VPN MODE to Server.
- Set the LAN/HOST MODE to LAN.
- Select the IKE VERSION. When IKE VERSION is set to IKEv2, you can enable or disable:
- MULTIPLE SA’S FOR IKEV2
- MOBIKE
- Select the AUTHENTICATION TYPE.
- After selecting Certificates, you must select any existing PEM Certificates on the router, or upload the certificate components to the router.
- After selecting PSK, you must enter a text string for the pre-shared key.
- Enter the PEERS as one or more IPv4 or IPv6 IP addresses.
- Enter LOCAL SUBNETS, REMOTE SUBNETS and any EXEMPT SUBNETS.
- Enter LOCAL AUTHENTICATION ID and REMOTE AUTHENTICATION ID to match the credentials for your VPN server.
- Select the WAN INTERFACES for VPN traffic to and from the router, in order of priority.
- Select whether to START the tunnel when you finish configuration and click CREATE.
- Configure DEAD PEER DETECTION, if desired (requires you to configure the SECONDARY PEER FOR FAILOVER).
- Configure IKE settings.
- Select whether to use PERFECT FORWARD SECURITY (PFS).
- If PFS is enabled, configure ESP settings.
- Click CREATE.
Configuring a HOST-to-LAN tunnel in Server mode
The settings in the procedure below are described in the IPsec Configuration Settings table above.
To configure a HOST-to-LAN tunnel in Server mode:
- Enter a tunnel NAME.
- Set the router’s VPN MODE to Server.
- Set the LAN/HOST MODE to HOST.
- Enable or disable USE DEFAULT VIRTUAL IP POOL(S).
- Enter the VIRTUAL IP ADDRESS POOL(S) (IPv4 or IPv6), if you have disabled USE DEFAULT VIRTUAL IP POOL(S).
- Select the IKE VERSION. When IKE VERSION is set to IKEv2, you can enable or disable:
- MULTIPLE SA’S FOR IKEV2
- MOBIKE
- Select the AUTHENTICATION TYPE.
- After selecting Certificates, you must select any existing PEM Certificates on the router, or upload the certificate components to the router.
- After selecting PSK, you must enter a text string for the pre-shared key.
- Enter the PEERS as one or more IPv4 or IPv6 IP addresses.
- Enter LOCAL SUBNETS and any EXEMPT SUBNETS.
- Enter LOCAL AUTHENTICATION ID and REMOTE AUTHENTICATION ID to match the credentials for your VPN server.
- Select whether to START the tunnel when you finish configuration and click CREATE.
- Configure DEAD PEER DETECTION, if desired (requires you to configure the SECONDARY PEER FOR FAILOVER).
- Configure IKE settings.
- Select whether to use PERFECT FORWARD SECURITY (PFS).
- If PFS is enabled, configure ESP settings.
- Click CREATE.
VPN Failover
To use VPN failover to help maintain your VPN connection, set DEAD PEER DETECTION (DPD) to Failover, and configure a secondary VPN peer. Dead Peer Detection (DPD) verifies the status of the active connection. For example, if the primary/active VPN goes down (that is, DPD detects that the end device is not responding), you can configure the VPN to automatically switch traffic to a backup VPN tunnel (the secondary peer).
By default, Dead Peer Detection begins 30 seconds after no incoming traffic is detected. After five retries at 30-second intervals (by default), traffic failure is confirmed. VPN traffic then “fails over” to the backup VPN tunnel.
The number of retries is not configurable, and the interval can be a minimum of 30 seconds.
After failover, the secondary peer becomes the primary. If the original primary peer comes back online, the VPN does not automatically switch back until another transmission failure is detected and failover happens again. Rebooting the router also restores the primary peer, if it is online.

Multi-WAN Policies
After you have created an IPsec VPN tunnel, you can add the tunnel to a Multi-WAN rule to help steer and optimize how the tunnel uses its assigned WAN interfaces.
Under Multi-WAN Policies, the IPSEC POLICIES FOR CLIENT TUNNELS table displays your configured VPN tunnels, with each tunnel’s configured WAN outputs, in priority, and the WAN interface that is currently active.

You can apply any Multi-WAN Rule (Roaming, Signal Strength, Wi-Fi SSID, or Speed) to a VPN tunnel to influence which WAN interface the VPN uses. For more information on Multi-WAN Policies, see Configuring Multi-WAN Policies.
Only IPsec VPN tunnels that have a custom ordering of WAN interfaces (configured in WAN INTERFACES as described in the IPsec Configuration Settings table) appear in the IPSEC POLICIES FOR CLIENT TUNNELS table.
IPsec VPN tunnels that use the default WAN zone do not appear in the IPSEC POLICIES FOR CLIENT TUNNELS table. Instead, they use the Default IPv4 Traffic or Default IPv6 Traffic System Policies, which by default use the default WAN zone.
You can view the default WAN zone interface priority under Networking > Zones Settings > SYSTEM ZONES.
If you want to modify the default WAN priority, click the WAN Output(s) field for the Default IPv4 Traffic or Default IPv6 Traffic Policies, and add interfaces to that policy. Alternatively, you can create a new Zone containing the interfaces in the priority you want. Click CREATE, and add interfaces or LAN segments in the desired order.
You can then add the modified Multi-WAN System policies to Multi-WAN rules to control how the IPsec VPN tunnels use their assigned WAN interfaces.